Your Guide to Post-Quantum Cryptography (PQC) [2026 update]
AI summary
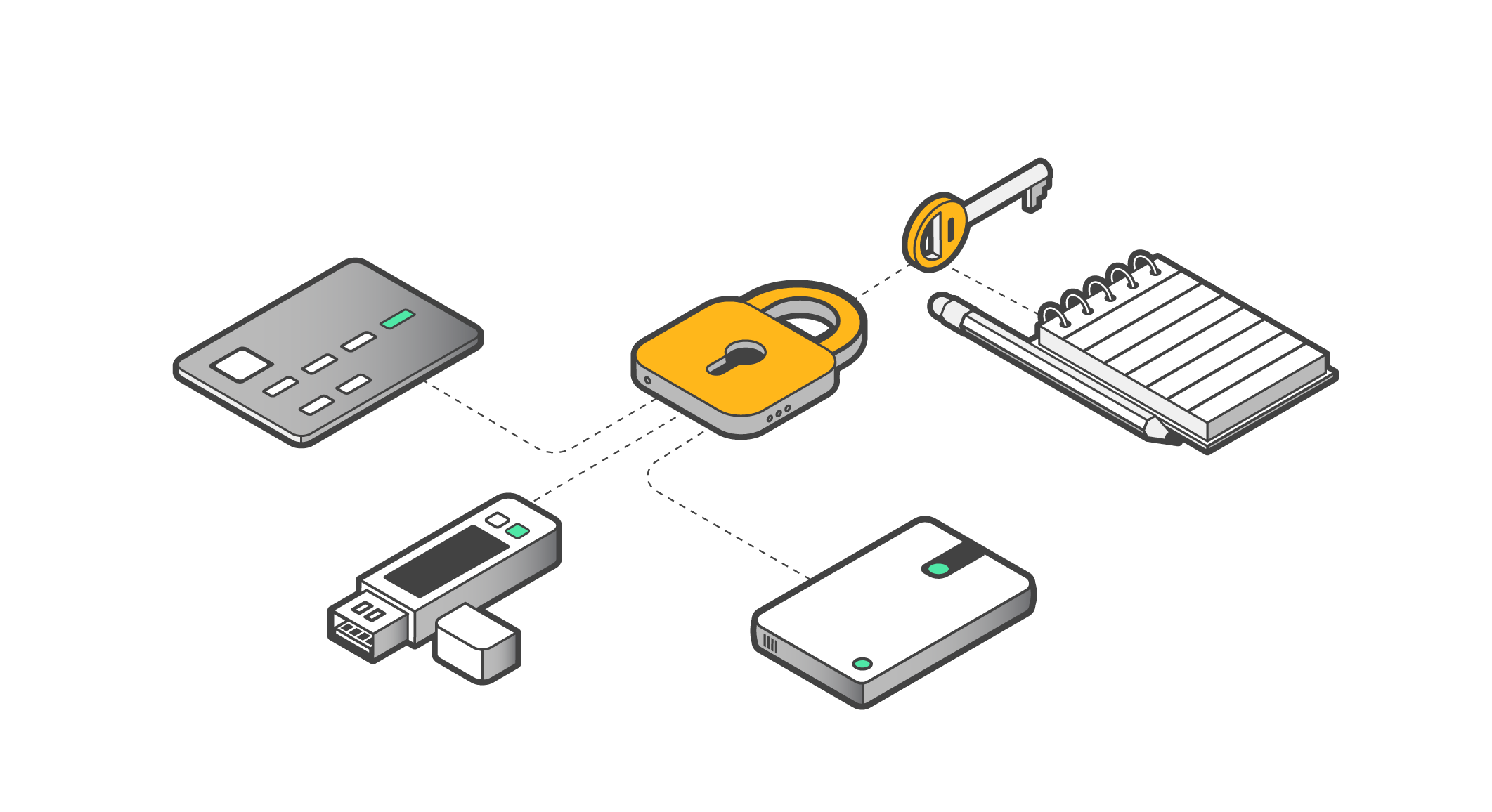
Every crypto wallet has two keys: a public key (think of it like your email address, shareable with anyone) and a private key (think of it like your password, which only you should ever know). When you send crypto, your wallet uses the private key to create a digital signature that proves you authorized the transaction.
The entire security of this system relies on one idea: it's practically impossible to determine a private key from a public key. The math behind this is called Elliptic Curve Cryptography (ECC), specifically the ECDSA (Elliptic Curve Digital Signature Algorithm). Bitcoin, Ethereum, and most major blockchains use it.
With today's computers, cracking a private key from a public key using ECC would take longer than the universe has existed. So we've been comfortable. The problem is, quantum computers don't play by the same rules.
What is a Quantum Computer?
A regular computer stores information as bits: either a 0 or a 1. Everything your laptop does, every calculation, every web page, every game, is just millions of 0s and 1s flipping back and forth at high speed.
A quantum computer uses qubits, which can be 0, 1, or both at the same time, thanks to a quantum property called superposition. Another property, called entanglement, allows qubits to influence each other instantaneously. The result: a quantum computer can explore a massive number of possible answers to a problem simultaneously, rather than checking them one at a time.
For most everyday tasks, this doesn't matter. But for certain math problems, especially those on which cryptography relies, it changes everything.
Shor's Algorithm
In 1994, Peter Shor figured out that a sufficiently powerful quantum computer running what's now called Shor's Algorithm could break the math behind both RSA encryption and Elliptic Curve Cryptography.
In plain terms, a powerful enough quantum computer could work backwards from your public key and figure out your private key. Not in trillions of years, but potentially in hours or days. Learn more about how private and public keys work.
How Real Is the Quantum Threat to Crypto?
It's not an immediate danger, but it's no longer science fiction. Currently, no quantum computer exists that can crack Bitcoin's cryptography. The machines researchers build today are still too error-prone and too small. Cracking Bitcoin's ECDSA keys would require millions of stable, error-corrected qubits. The best machines today are far from that.
But timelines are shrinking. Google, IBM, Microsoft, and dozens of national governments are pouring billions into quantum research. A survey of global experts found that roughly a third believe there's a 50% or greater chance that a cryptographically relevant quantum computer (a CRQC) could emerge between 2029 and 2035.
Harvest Now, Decrypt Later
Even if a working CRQC is still a decade away, bad actors can collect encrypted data and public keys today and just wait. When quantum machines become powerful enough, they decrypt everything they've been sitting on.
For crypto, this is especially relevant because blockchains are permanent and public. Every transaction ever made, including the public keys linked to those transactions, is recorded forever on-chain. Any address that has ever sent a transaction has already exposed its public key to the entire world.
About 6.9 million BTC (roughly one-third of the total supply) already sit in wallets with exposed public keys, making those coins theoretically vulnerable once a CRQC arrives. This includes many early Bitcoin addresses, exchange wallets that reuse addresses, and Satoshi Nakamoto's estimated 1.1 million BTC, which have sat untouched since 2010.
What is Quantum-Resistant Cryptography?
Quantum-resistant cryptography (also called post-quantum cryptography, or PQC) refers to cryptographic algorithms designed to remain secure even against attacks from quantum computers.
The keyword is "designed." These are not existing algorithms that developers have patched to be stronger. They're fundamentally different kinds of math that quantum computers struggle with just as much as regular computers do.
Lattice-Based Cryptography
This is the leading approach right now. It relies on the extreme difficulty of solving problems involving high-dimensional geometric structures called lattices. Even quantum algorithms don't have a known efficient way to solve them. Think of it like trying to find a specific point in a multi-thousand-dimensional grid with no map.
Hash-Based Cryptography
This approach builds signatures out of cryptographic hash functions. Hashing is considered relatively robust against quantum attacks. Hash-based signature schemes like SPHINCS+ are already standardized.
Code-Based Cryptography
This method is based on error-correcting codes, the same mathematical structures used to reliably transmit data over noisy channels. The underlying problem, known as syndrome decoding, has resisted cryptanalysis for decades and remains immune to known quantum algorithms. It's one of the oldest families in post-quantum research, predating the current NIST process by nearly 50 years.
The NIST Standards
In August 2024, after an eight-year international competition evaluating 82 algorithms from 25 countries, the US National Institute of Standards and Technology (NIST) officially published its first three post-quantum cryptography standards:
- ML-KEM (Module-Lattice-Based Key-Encapsulation Mechanism), based on the CRYSTALS-Kyber algorithm, for key exchange.
- ML-DSA (Module-Lattice-Based Digital Signature), based on CRYSTALS-Dilithium, for digital signatures.
- SLH-DSA (Stateless Hash-Based Digital Signature), based on SPHINCS+
NIST has urged organizations to begin migrating to these standards now, not later. Companies like Apple, Cloudflare, and AWS have already started rolling out quantum-resistant encryption in their products.
The crypto space is moving more slowly, partly because blockchains require a broad community consensus for any protocol changes. Check out the top 7 quantum-resistant coins to monitor.
PQC: Where Does the Crypto Industry Stand?
Bitcoin
BIP-360 proposes introducing quantum-resistant address formats, but Bitcoin's governance model is notoriously conservative, which is both a strength and a challenge here. Moving the entire Bitcoin network to new cryptographic standards requires coordination across developers, miners, exchanges, and millions of users. Estimates suggest this process could take 5 to 10 years, even after consensus is reached.
Ethereum
The Ethereum Foundation published a formal post-quantum roadmap in February 2026. Vitalik Buterin has outlined that validator signatures, data storage, accounts, and proofs all need to change. The proposed path involves a protocol-wide transition to PQC, likely a hard fork, with account abstraction as the mechanism for migrating user wallets.
Solana
Less formal than Ethereum's approach. Solana developers introduced a quantum-resistant vault using Winternitz hash-based signatures, a one-time signature scheme that limits exposure of the public key. It's opt-in, not protocol-level, meaning users have to actively migrate funds into the vault structure. It's a meaningful step but not a comprehensive solution. No full protocol-level PQC migration plan has been published as of March 2026.
Ripple
In December 2025, XRPL's AlphaNet activated a full suite of quantum-resistant features: Quantum Accounts, Quantum Transactions, and Quantum Consensus, all built around CRYSTALS-Dilithium. However, it's still on the developer network, not mainnet.
Frequently Asked Questions
Is quantum computing an immediate threat to my Bitcoin today?
No quantum computer currently exists that can break Bitcoin's cryptography. The consensus among experts is that a threat at this scale is still 5 to 15 years away, possibly longer.
If Bitcoin upgrades to post-quantum cryptography, will my old wallet still work?
It depends on the implementation. Any significant cryptographic upgrade to Bitcoin requires users to migrate their funds to new address formats.
What makes a coin quantum-resistant?
A coin is quantum-resistant if its underlying signature and encryption algorithms are designed to be computationally hard for both classical and quantum computers. Most use lattice-based or hash-based schemes rather than elliptic curve math. CRYSTALS-Dilithium, Kyber, FALCON, and SPHINCS+ are among the algorithms now standardized by NIST for this purpose.
Does using Tangem make my Bitcoin quantum-proof?
No. If Bitcoin itself doesn't upgrade its signature scheme at the protocol level, the long-term quantum-signature vulnerability persists. Tangem is the best wallet-level protection available today, but it can only do what the underlying blockchain allows.
What is "harvest now, decrypt later"?
It's a type of attack where bad actors collect and store data today, before they can break it. Once quantum computers are powerful enough, they will be able to decrypt the stored data. For crypto, this means sophisticated adversaries are collecting public keys and transaction data already recorded on public blockchains.
Are there any hardware wallets with built-in post-quantum algorithms?
At the wallet hardware level, no major consumer hardware wallet has shipped with post-quantum signing algorithms for Bitcoin or Ethereum yet, mainly because those blockchains themselves have not adopted PQC standards.